Cyber Security
Enabling a bright future for technology
The home care sector is positioned to respond to the increasing demand for care at home and is challenged with workforce resource shortages that were worsened during the COVID 19 pandemic. Technology can help alleviate that workforce pressure if attention is paid to privacy protection and cyber security.
Cyber security is more than just technology. A comprehensive cybersecurity strategy includes policies, procedures, user education, risk management, and incident response planning. Effective cybersecurity requires a holistic approach that involves all aspects of an organization, from the c-suite to individual employees. Cyber security must be a key pillar of any organization, regardless of size, that uses technology. Security requires constant vigilance and is a complex undertaking in home care where health data needs to be accessible everywhere and in being ubiquitously available, that data is at risk. The goal must be to strike the balance of making mobile and home health technology easy for the right people to access but hard for hackers to break into.
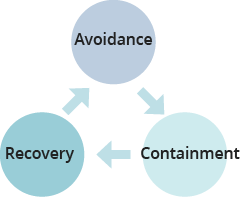
Data protection is increasingly complex. It involves building defences, monitoring for attempts to breach data, and having the resilience to recover quickly and improve.
Avoidance
Building defences to keep hackers out and avoid a breach of the network includes strategies such as:
- Implementing strong passwords and regularly updating them.
- Using multifactor authentication (MFA) whenever possible. MFA is a security process that requires users to provide two or more forms of identification.
- Keeping software and systems up to date with the latest patches and security updates

- Conducting regular backups. In the home and community care sector where data is spread across the community, cloud solutions can be a robust secure foundation. However, the cloud is a relatively new option and moving from on-premises requires a skills transition to understand different risks and controls.
- Data encryption, the process of converting plaintext into ciphertext, which is unreadable without a key, to protect data from unauthorized access or modification.
- Air gapping which is basically the concept of segregating infrastructure so that if one part is compromised, the whole system is not. The idea is to isolate within the large system the specific information that’s higher risk preventing one compromised asset from infecting the whole the whole environment.
- Employee education on cyber security best practices and identifying potential threats
- Conducting regular security assessments and penetration testing to identify vulnerabilities
The single biggest vulnerability for cyber-attacks is the social engineering side – the well-crafted phishing e-mail that gets somebody to click and do something inadvertent. Education and awareness are the best strategy. Monthly cyber awareness training and phishing tests for all staff must be the habit and this should be supported by a culture of learning not “gotcha”. At HIROC we track the results of our tests and report back to all staff, so everyone gets better at spotting and avoiding the attack.
Containment
The goal of containment is to prevent the spread of a security incident and to minimize the damage caused. It’s important to have a well-documented incident response plan in place before an intrusion occurs, so that staff know what steps to take and who to contact in the event of a breach.
Regularly monitoring network activity for anomalous behaviour serves to detect and respond to security incidents as quickly as possible. Network monitoring tools can include firewalls, intrusion detection systems (IDS), and security information and event management (SIEM) software. These tools can help security teams to identify and respond to potential threats, track network performance and traffic, and provide real-time visibility into network activity.
Firewalls act as a barrier between a private internal network and the public Internet, helping to protect against unauthorized access, hacking attempts, and other security threats.
IDS, which these days are starting to blend with antivirus systems, protect the end point. This enables catching and containing an inadvertent download, from a phishing attempt for example, before it goes any further than the single device and sometimes can even stop the device from being compromised.
SIEM is essentially a technology that conducts real-time monitoring and analysis. The system listens to signals, watches log files from everywhere, from every device, from anything or anyone and uses artificial intelligence based on patterns to detect problems.
If there is suspicion that the network has been compromised by an intruder, the goal is to stop the spread of the security breach and limit its impact. This will involve isolating affected systems and taking remediation measures.
Recovery
No matter how robust the systems, it is a matter of when, not if, a breach may happen. Recovery is the process of restoring normal operations as quickly as possible after a security incident has been contained.
It is vital to have a sound incident response plan that includes a communication strategy, business continuity plan and a disaster recovery plan. Backups are part of a disaster recovery strategy and therefore need to be conducted as frequently as the organization can stand to lose its data. That may mean hourly or more for some systems and less frequently for others.
Plans need to be exercised, incidents simulated, and recovery protocols practiced so the organization is in the habit of continuing without a glitch if compromised.
The Home Care Challenge
The structure of the home and community care sector creates unique challenges in cyber security. There are thousands of organizations providing care and support to individuals in the community. Many of these would not have the means to scale and invest individually in tools and/or people to manage cyber security to the level required in today’s environment. A way forward could be through collaboration amongst organizations to engage security guidance and protection – potentially a security operations centre supporting dozens of home and community care agencies. The role for government could be a level of certification attesting to the requisite cyber security measures in place.
Notwithstanding…
Cyber security and privacy should not scare anyone. It’s not hard. It requires diligence and caution, but my advice is to put on the hard hats and go for it. It is right for patients, for caregivers, and for everyone.
References
[i] Office of the Privacy Commissioner of Canada. (2014) Privacy and Cyber Security, Emphasising privacy protection in cyber security activities. Ottawa. P2. Retrieved from https://www.priv.gc.ca/media/1775/cs_201412_e.pdf
[ii] [ii] Burke, D. (2020). Hospitals ‘overwhelmed’ by cyberattacks fuelled by booming black market. CBC News Retrieved from https://www.cbc.ca/news/canada/nova-scotia/hospitals-health-care-cybersecurity-federal-government-funding-1.5493422
[iii] Why Do People Fall For Phishes? (Brit Insurance) Retrieved from: https://www.hiroc.com/resources/why-do-people-fall-phishes-brit-insurance



